 The other day I grabbed my keys for work and noticed my USB drive was missing from the keychain. Apparently I was no longer traveling with my SanDisk DataTraveler drive and I had no idea where I had lost it. Worse, I had no idea who had found it. A moment of panic came over me until I found the drive nestled behind some junk on the kitchen table where I had dropped my keys earlier. The plastic arc that connects the drive to my keychain had simply snapped off.
The other day I grabbed my keys for work and noticed my USB drive was missing from the keychain. Apparently I was no longer traveling with my SanDisk DataTraveler drive and I had no idea where I had lost it. Worse, I had no idea who had found it. A moment of panic came over me until I found the drive nestled behind some junk on the kitchen table where I had dropped my keys earlier. The plastic arc that connects the drive to my keychain had simply snapped off.
In that moment of panic a million questions ran through my mind:
- What is currently on that drive?
- Is it sensitive information?
- What was on that drive that could be recovered by someone who knows how undelete files?
Lesson learned: Encrypt any and all USB drives that will leave the office.
I pulled up a program called TrueCrypt which I had used to encrypt some sensitive files to send to a client a few years back. TrueCrypt has a neat little feature where you can install the software on the drive as a traveling device so that you can run it without having to install the software on the guest computer. This is handy if you’re giving a presentation on someone else’s laptop or need to access your files from a public computer but don’t have admin rights to install new software.
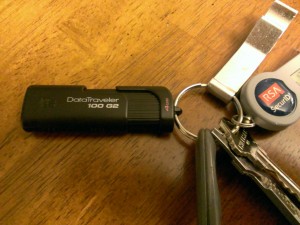
I snagged a new DataTraveler drive from my drawer and a few mouse clicks later and I had an encrypted 3GB storage component based on some serious encryption that would keep hackers (and foreign governments) busy for quite a few years. Given that the USB drive only contains a PowerPoint presentation that I was going to give the next day, it probably isn’t worth the time to brute force the password! But I know that should I have to transfer a files of any sensitive nature, I already have the protocols and practice in place to make sure it’s encrypted.
You can get You can download TrueCrypt from http://www.truecrypt.org/. Their documentation is very good (albeit a bit technical, but, hey, you’re talking encryption and that’s some nerdy stuff). There are plenty of resources out there detailing how to create encrypted drives and partitions, so I’ll skip that and just point you to the TrueCrypt site as a starter. I should mention that TrueCrypt has the ability to create a hidden encrypted volume inside of a visible encrypted volume where you use one of two passwords to open the encrypted file store that you need. Pretty slick if you’re really trying to hide something and fear you might be coerced into giving up one of the passwords.
Tips for creating an encrypted volume
Regardless of whether or not you’re using a single or double volume, here are some tips for creating an encrypted volume:
- Read the manual and understand the risks of the selections you make when creating your encrypted volume. There are some whitepapers on security sites demonstrating that volumes are less secure when the default TrueCrypt settings are used.
- Chose a long, complex password. This makes brute forcing a password much more time-consuming. Nothing is infinitely secure, but you can make it take hundreds of years to hack with the right combination of security and passwords.
- Encrypt everything and be in the habit of using an encrypted drive so that you don’t accidentally leave a sensitive file on the unencrypted drive.
I’m in no way affiliated with TrueCrypt. I know there are some other programs out there that do the same thing, but TrueCrypt is one of the easiest, most flexible, and lightweight solution that I’ve found. If you have other suggestions worth trying leave a comment below and I’ll check it out as well.